Choosing between a Vulnerability Scan and a Penetration Test
The terms "vulnerability scan" and "penetration test" are oftentimes mistakenly used interchangeably, even by people involved with IT. Moreover, our auditing team has faced incidents where a pentesting firm charges for a penetration test but actually delivers a vulnerability scan! The biggest concern of this misleading case is that you pay for a service with a name related to a higher security assurance (pentest) but you receive something with a comparatively lower assurance (vulnerability scan).
The Basics
| Vulnerability Scan | Penetration Test | |
|---|---|---|
| Definition | Involves usage of automated tools that scan for known vulnerabilities, targeting a single system, network or application. Also known as a vulnerability assessment. | Involves manual technical testing, usually by certified security professionals, that goes deeper than vulnerability scanning. The tests identify vulnerabilities on a system, network or application and continue further, attempting to exploit the detected vulnerabilities. Also known as a pentest or ethical hacking. |
| Similarities | Automated commercial or open-source tools are used to scan the target(s) and detect possible vulnerabilities. After the detection, a rating of each vulnerability is generated. |
A mixture of automated tools and manual exploitation techniques are used by the pentester. Automated tools which include service enumeration, host discovery and of course vulnerability scanning, are used to catch the low hanging fruit of the engagement. Manual exploitation requires the pentester to gather and interpret the findings from the automated tools to break into a system, a network, or an application. It also involves manual searching for vulnerabilities that automated scanners miss. |
| Differences | Only known vulnerabilities are discovered. No exploitation attempts against detected vulnerabilities is performed. Only confirmation and rating of the detected vulnerabilities. False positives sometimes occur which shall manually be examined and be excluded. | Exploitation attempts of the detected vulnerabilities are performed to verify their existence and usually, continue further in order to gain sensitive information. The whole procedure is a good simulation of a real-world scenario with an adversary targeting an organization. Thus, it provides a thorough view of your security posture. |
There are several regulations and standards that require penetration tests and vulnerability scans to be conducted regularly. Organizations regulated by ISO 27001, GDPR, ETSI, Webtrust, PCI DSS, HIPAA and others, usually require annual pentests in conjunction with quarterly vulnerability scanning. Make sure you understand what requirements organization is subject to and plan the assessments accordingly. SpearIT can also help you with consulting and ISO compliance & consulting services on the desired regulation or standard.
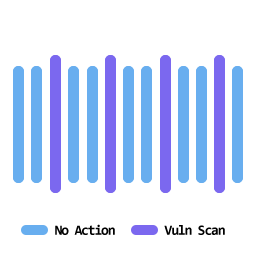
Vulnerability Scan
As a best practice, vulnerability scanning is recommended to be executed quarterly. However, based on your product's rate of changes and business criticality, a more frequent schedule should be applied, e.g. monthly. Additionally, it is recommended that new systems, devices, or applications that serve as a critical or sensitive component to the organization be scanned before going “live.” This allows an organization to verify that the new technology does not negatively impact the current cybersecurity posture of their environment.
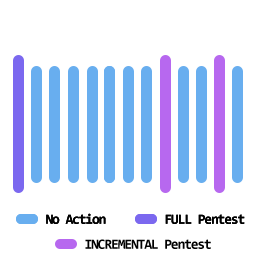
Penetration Test
It is recommended that pentests be conducted on an annual or even bi-annual basis. Similar to vulnerability scanning, laws and regulations have defined frequency requirements for organizations to comply. Reports with High or above findings after a pentest should be remediated as soon as possible, and then a retest should be conducted by a pentester to verify closure. It is also recommended that new, critical (or sensitive) systems, devices, or applications should be pentested before going “live.” This allows an organization to identify any High findings that a vulnerability scanning may not have otherwise captured
In case you are seriously interested and diligent regarding your organization's security posture, a combined approach of vulnerability assessment and penetration testing should be followed. Each of the two assessments is complimentary to the other and provide a holistic approach. Please keep in mind that SpearIT includes by default a comprehensive vulnerability scan in every penetration test option. For more information, have a look at the infrastructure and web-app pentesting options.
Both pentests and vulnerability scans provide a point in time snapshot of your cybersecurity posture. As the security landscape constantly evolves, with new threats appearing almost every day and as your software or systems are susceptible to changes, these assessments shall be conducted in a recurring manner.
Concerned about your cubersecurity posture?Our specialists are more than happy to discuss a solution with you!
Start Here!Latest News

Cypriot National eID becomes notified
